Capture live
Select an interface, start sniffing, and see packets land as the session unfolds.
Native macOS Packet Analysis
IceSniff puts live capture, packet drill-down, analysis sections, and a packet-aware AI rail into one fast native workspace.
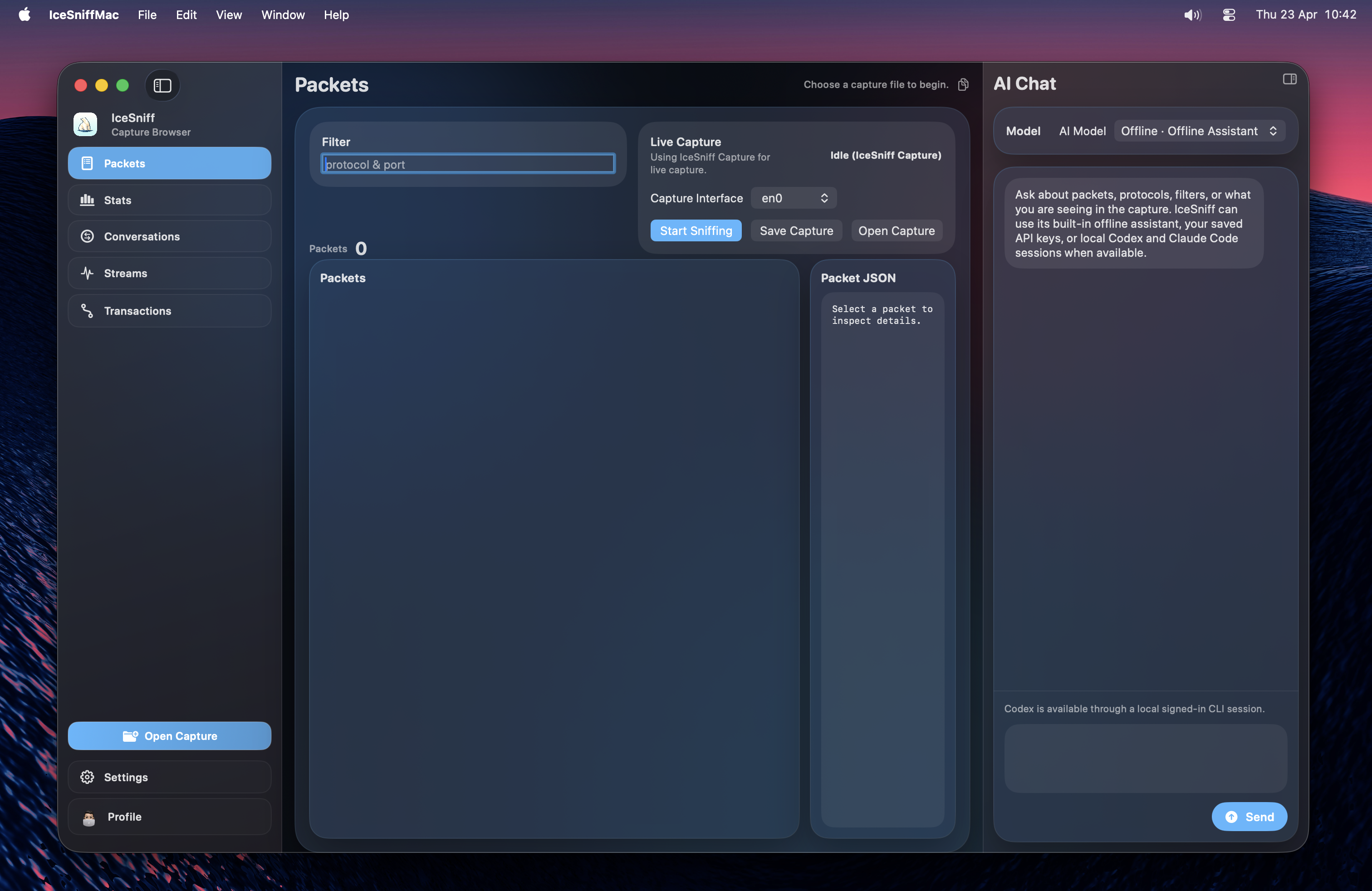
Workflow
Select an interface, start sniffing, and see packets land as the session unfolds.
Move from summaries to decoded fields, layer detail, and packet-aware context actions.
Open the right-side AI rail and reason over the selected packet without breaking focus.
Surface
Load existing captures directly into the native shell.
Start and stop capture from the same operational center.
Use comfort-first filters likehttp or 443.
Drill into decoded packet structure and byte-aware metadata.
Jump across conversations, streams, and transactions quickly.
Export the full capture or only the packets that match your filter.
Coverage
Ethernet, ARP, IPv4, TCP, UDP, and ICMP.
DNS, HTTP/1.1, and TLS handshake metadata.
Native macOS app, CLI, and a local web companion.
Shared Rust analysis engine with bundled capture helpers.